Discover Every Agent. Understand Every Action. Control What Happens Next.
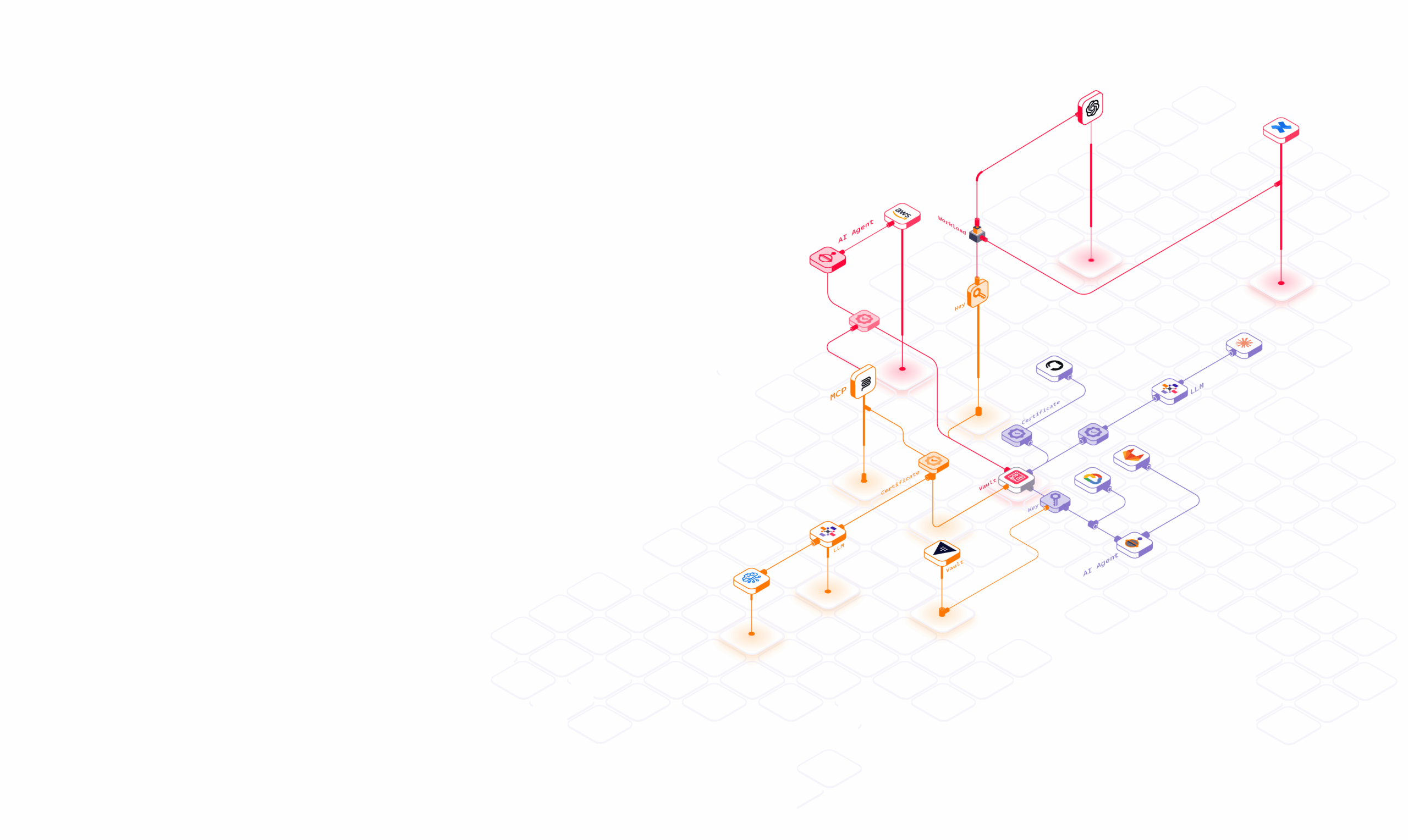
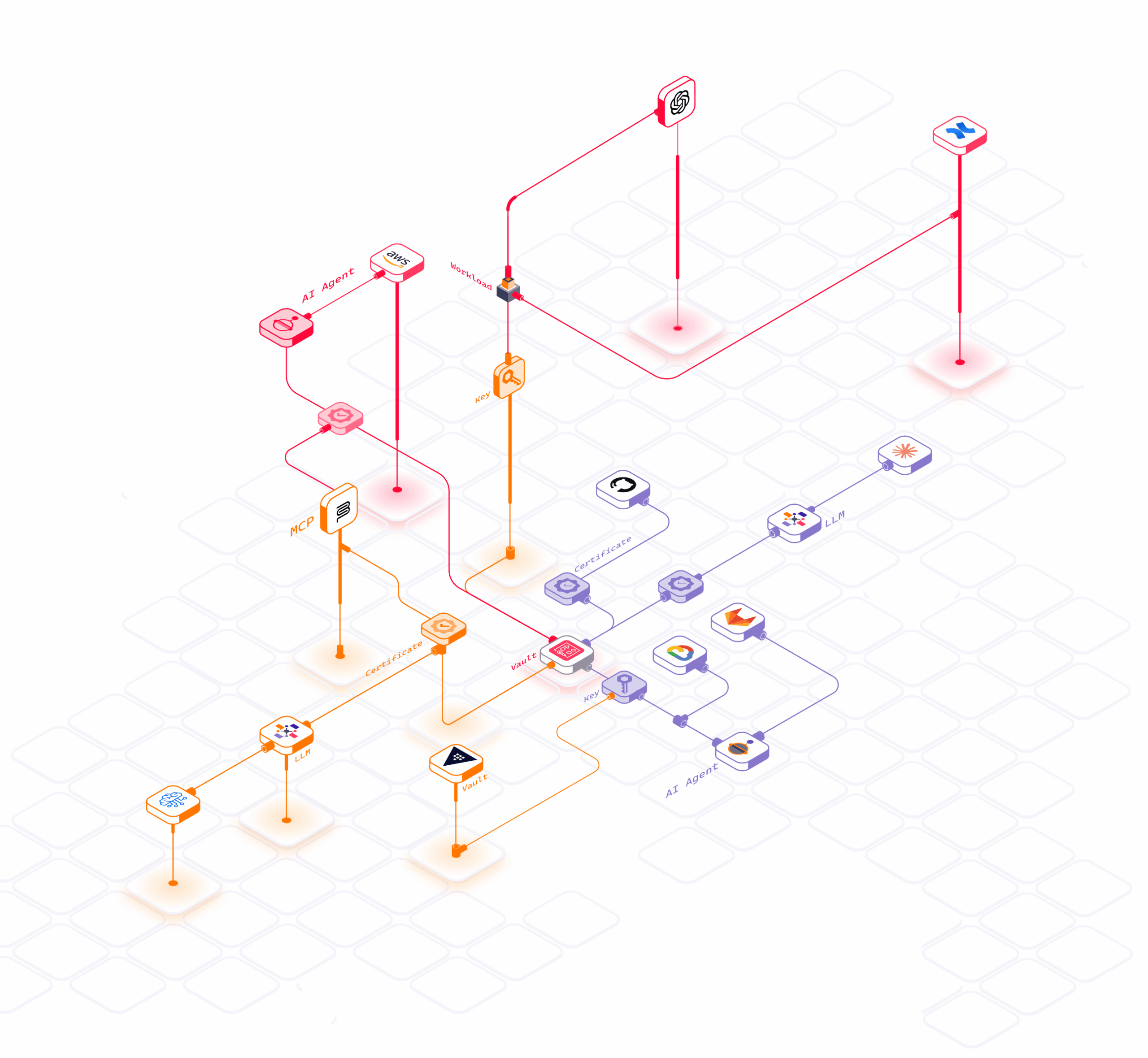
AI Agent & MCP Visibility and Governance
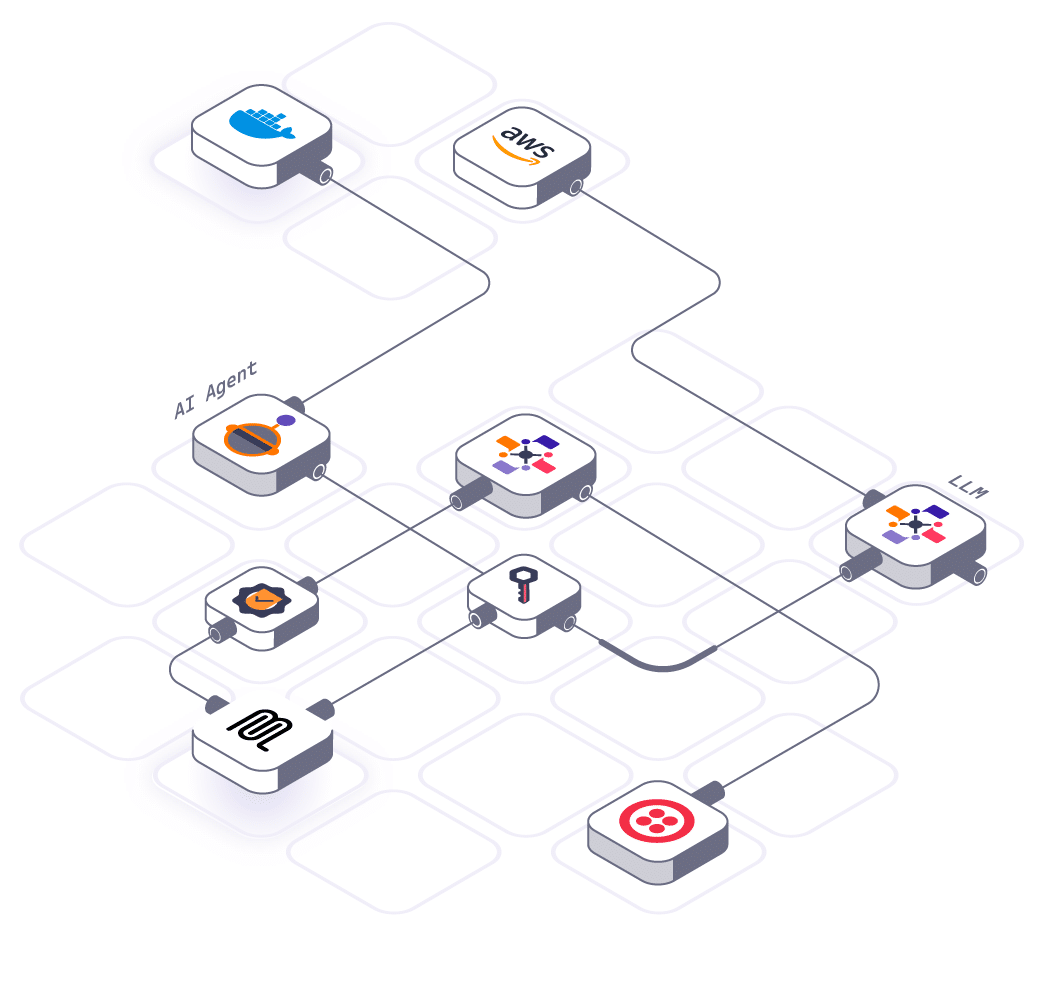
Hush Security maps agent-to-tool access across agents and MCP connections, then secures it with identity-based, policy-controlled access so you can govern agentic AI without static credentials.
The Challenge
AI agents are created fast, connect through MCP servers, and often rely on API tokens and embedded credentials, which leads to:
- Lack of visibility into what AI agents and MCP servers are running, where they’re deployed, and who owns them
- Blind agent-to-tool access, teams can’t see what agents can reach or do
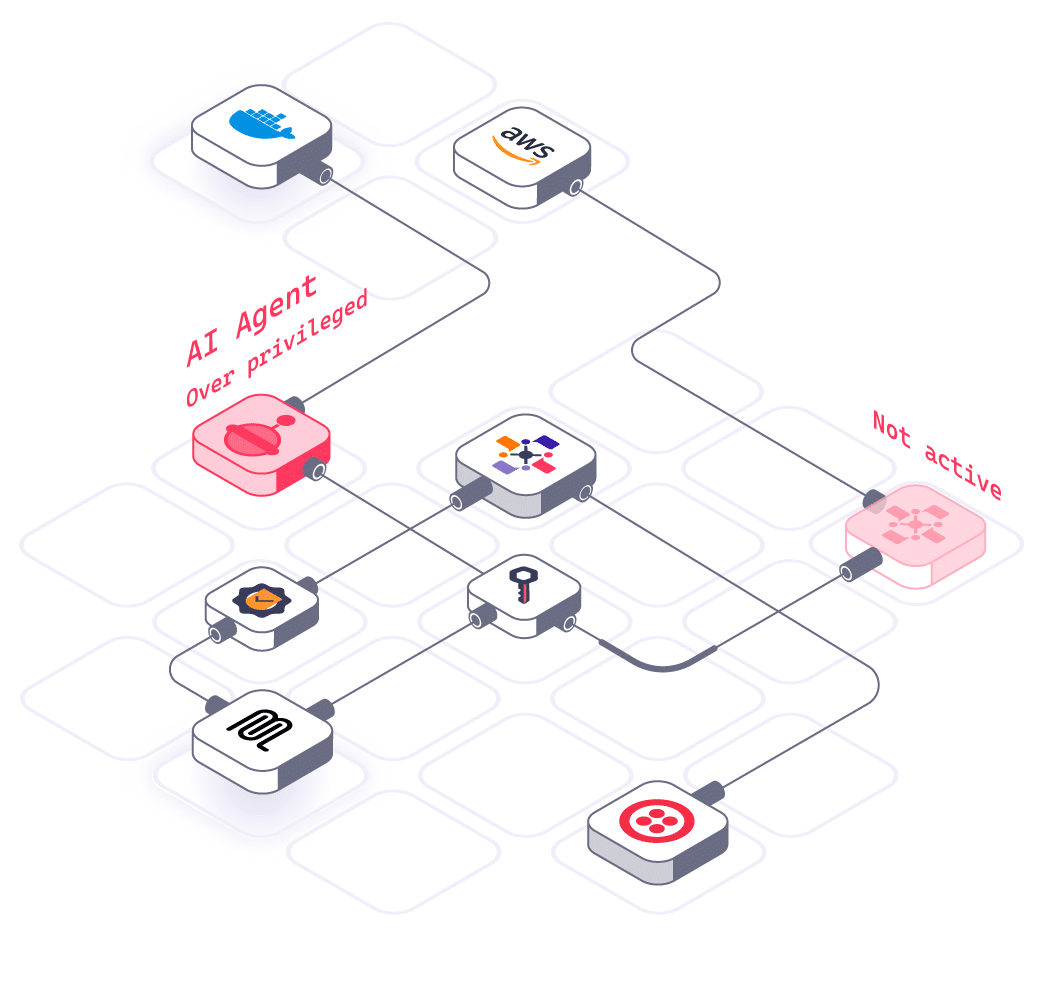
- Over-privilege and leaked tokens, expanding blast radius and exposure
- No runtime governance, making agents a fast-growing, high-privilege attack surface
The Solution
Continuous Agent and MCP Discovery with Real Governance
Hush Security combines continuous discovery with live identity telemetry for agents and MCP connections. We automatically find AI agents, map the tools and systems they can access, and surface the risky combinations that create real exposure.
Discover Everything Across the Enterprise
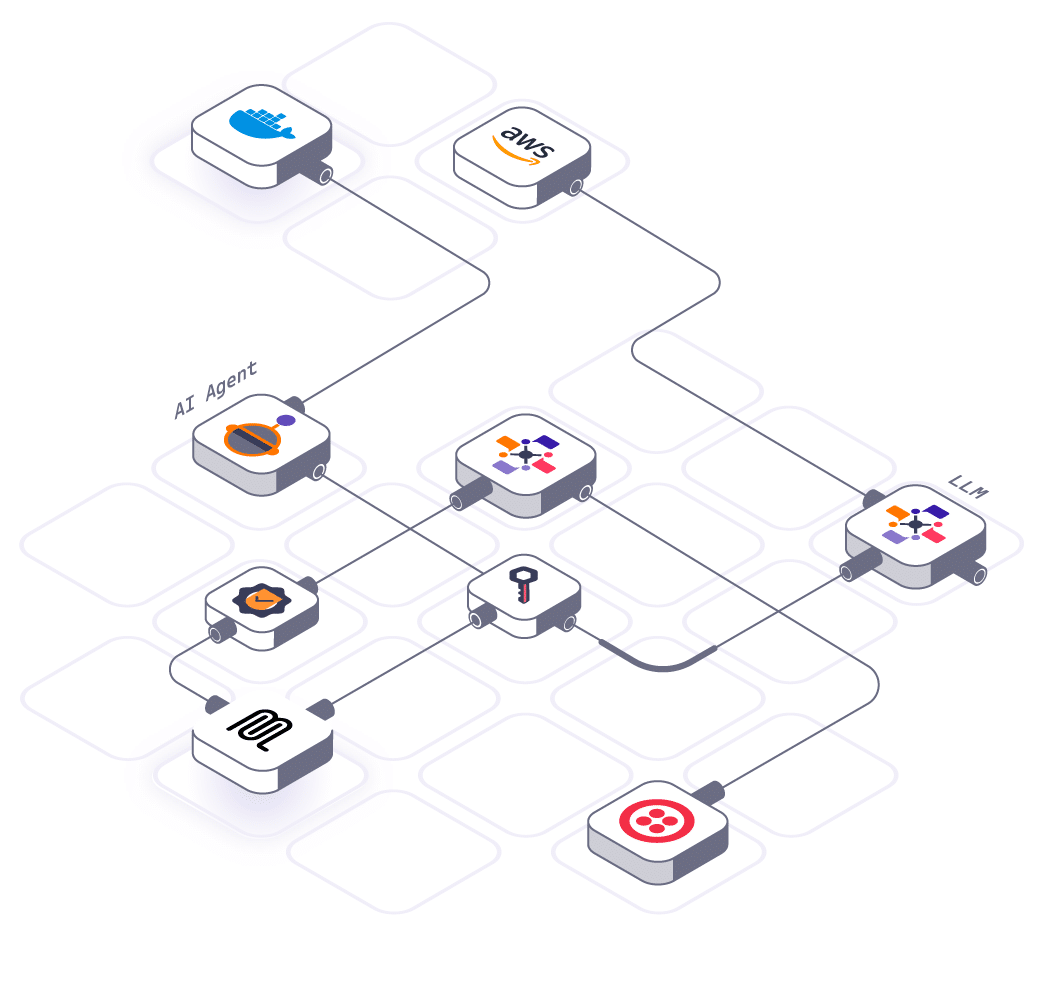
Automatically discover AI agents and MCP exposure across:
- AI agent frameworks, orchestration layers, and internal agent services
- MCP servers, tool connectors, and agent-to-tool integrations
- SaaS, cloud, and on-prem applications agents interact with
- CI/CD pipelines, automation tools, and ephemeral workloads
Runtime-Aware Governance for Agents and MCP
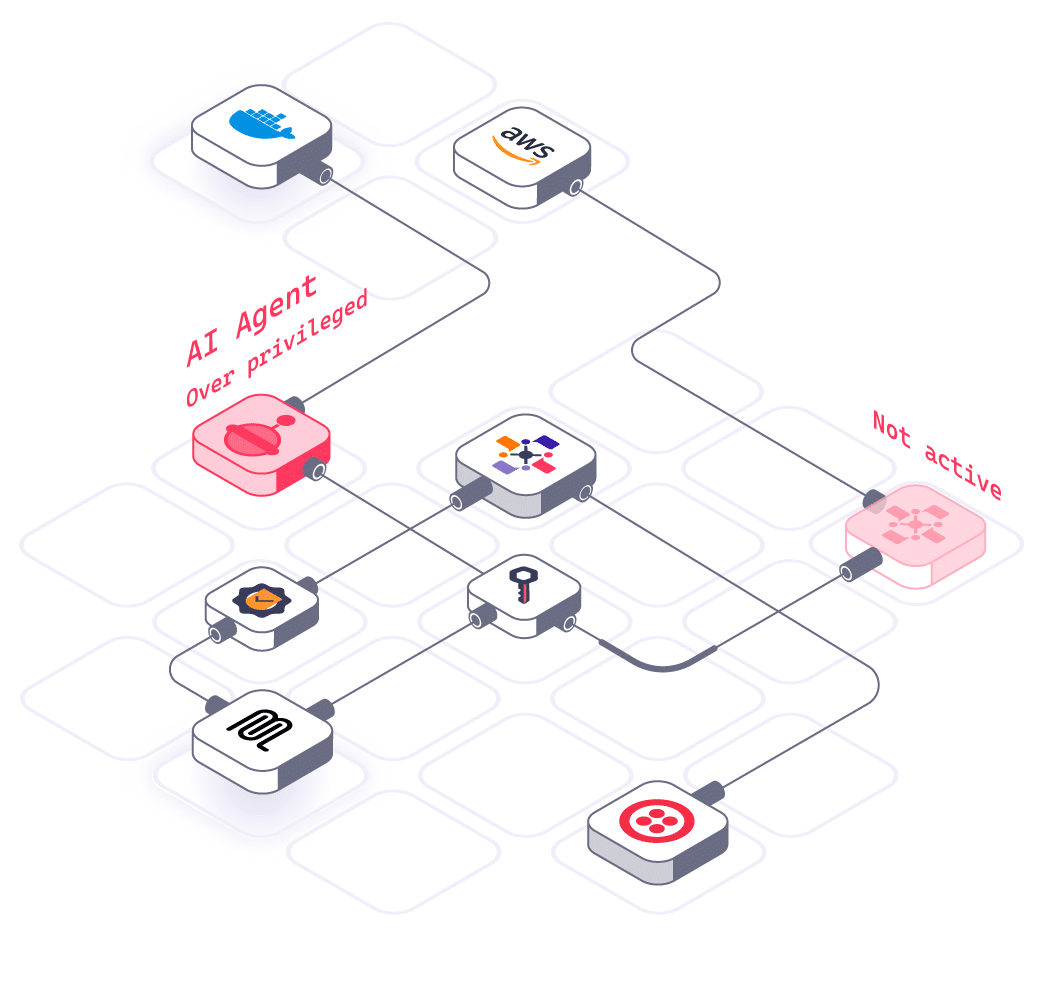
Govern agent risk by understanding and controlling:
- Which agents are active and how frequently they operate
- Over-privileged agents and risky toolchains (high-impact combinations)
- Orphaned, experimental, or unowned agents that persist over time
The Value
 Continuous Discovery
Discover agents and MCP connections continuously, not once
Continuous Discovery
Discover agents and MCP connections continuously, not once
 Risk Prioritization
Identify the agents that matter by focusing on real exposure and privilege
Risk Prioritization
Identify the agents that matter by focusing on real exposure and privilege
 Policy Enforcement
Prevent agent-driven incidents by tightening access and enforcing policy
Policy Enforcement
Prevent agent-driven incidents by tightening access and enforcing policy
 Fast Time to Value
Move fast with lightweight deployment and fast time to value
Fast Time to Value
Move fast with lightweight deployment and fast time to value