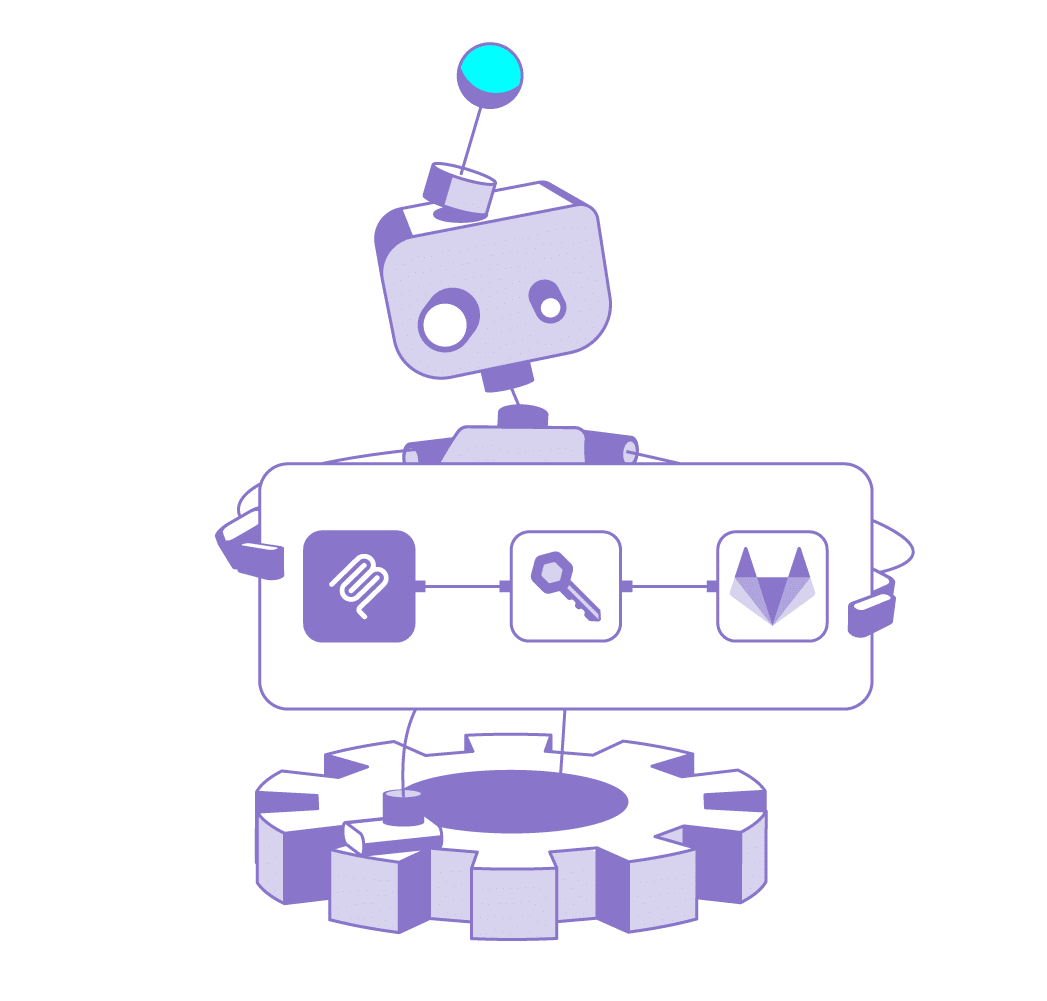
End-to-End Control for Non-Human Identities
From Creation to Retirement. Without Manual Effort.
Manage NHI lifecycle the easy way - with simple policies that do the work for you. Create with the right permissions, keep governance continuous while in use, and retire NHIs the moment they are no longer needed.

The Challenge
Non-human identities are created constantly.
CI jobs spin up service accounts. Cloud workloads generate tokens. AI agents authenticate dynamically. Certificates and secrets are issued for short-lived tasks, but rarely removed on time.
In most organizations, lifecycle management is fragmented or entirely manual:
- Creation happens through scripts, pipelines, or ad-hoc processes
- Permissions drift over time as usage changes
- Rotation, revocation, and cleanup rely on brittle schedules or human intervention
The Solution
Hush Security automates the entire NHI lifecycle through a disruptive, policy-first access model.
Instead of managing identities with manual rotation schedules and recurring credential work, you simply define a policy. Hush enforces it continuously, using real usage and runtime behavior to keep access right-sized by default. Creation is as simple as defining an IAM role in a major cloud provider: set the intent and boundaries, and the identity is provisioned with least privilege from day one.
Joiner - Spin Up Right, By Default
Define a policy once, like defining an IAM role, and Hush provisions the NHI right-sized by default with least privilege from day one.
- Define intent as policy – as simple as creating an IAM role in a major cloud provider.
- Right-sized from day one – least privilege by default, not after-the-fact cleanup.
- Guardrails included automatically – ownership, scope, and constraints applied at creation without tickets or custom scripts.
Mover - Stay Right-Sized as Reality Changes
- Continuously evaluate real usage – policies track what the identity actually does at runtime, not what it was configured to do.
- Auto right-size permissions – expand or reduce access safely as behavior changes, with least privilege maintained by default.
- Replace reviews and rotation schedules – policy-driven governance makes adjustments continuously without breaking workloads.
Leaver - Shut It Down the Moment It’s Done
- Detect when it is truly unused – policies identify inactivity based on runtime signals, not stale inventory.
- Decommission safely, in context – validate dependencies and impact before taking action, so nothing breaks.
- Revoke and retire automatically – remove access and credentials immediately, eliminating orphaned NHIs and shrinking the attack surface fast.
The Value
 Zero Manual Work
Eliminate manual NHI lifecycle work
Zero Manual Work
Eliminate manual NHI lifecycle work
 Attack Surface Reduction
Reduce attack surface by retiring unused identities automatically
Attack Surface Reduction
Reduce attack surface by retiring unused identities automatically
 Risk Reduction
Improve security without slowing engineering teams
Risk Reduction
Improve security without slowing engineering teams
 Operational Efficiency
Cut operational burden by eliminating rotations and manual lifecycle workflows
Operational Efficiency
Cut operational burden by eliminating rotations and manual lifecycle workflows